
Keep Your Computer Running Smoothly with Professional Repairs in Brisbane
Is your computer acting up? Has it slowed down significantly or started making strange noises? If that’s the case, you

Is your computer acting up? Has it slowed down significantly or started making strange noises? If that’s the case, you

What is a computer? It is a technology-driven device that allows us to access and use information from the internet

What is Smart Bridge? Smart Bridge is a technology that allows devices to communicate with each other. It is used

For the users of Microsoft Outlook, a Outlook Mail Merge is an efficient way to send personalized messages or documents

What is Terminal Proxy? Terminal Proxy (sometimes referred to as “proxy”) is a computer networking term that refers to using

When it comes to file hosting sites, there are a lot of different options to choose from. Each site has
When it comes to finding a good file hosting site, choosing between a few different options can be difficult. However,

For many PC gamers, playing on a monitor is the best way to experience games. However, before you go out

Lenovo is a well-known company that specializes in cheap laptops. It’s not uncommon to see their products on sale, but
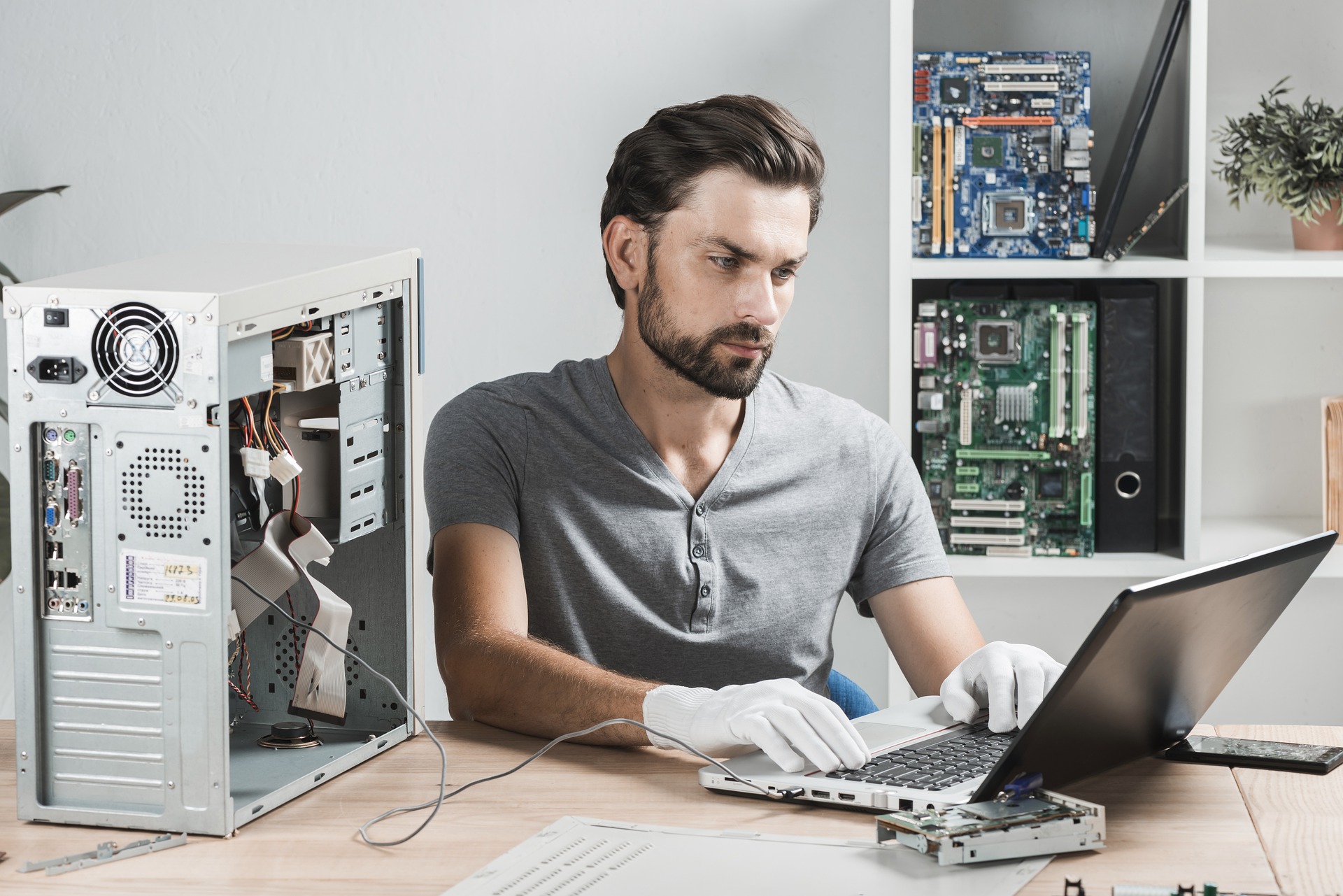
You will need fast laptop repair Penrith services because this system is used a lot. You cannot live without a